According to abbreviationfinder, WAP is an acronym for Wireless Application Protocol, a secure standard that allows users to access information instantly through wireless devices such as PDAs, mobile phones (walkie-talkies) and smart phones (smartphones).
Concept
The WAP standard supports most wireless networks, including CDPD, CDMA, GSM, PDC, PHS, TDMA, FLEX, ReFLEX, iDEN, TETRA, DECT, DataTAC, and Mobitex and is supported by all operating systems.
WAPs that use screens and have Internet access use what are called micro browsers, browsers with small files, which can be adapted to the restrictions of small memory and low bandwidth that devices that use this standard have.
Although WAP supports HTML and XML, the WML language (an XML application) has been developed specifically for small screens and with one-handed navigation without a keyboard. WAP also supports WMLScript, similar to Javascript, but with minimal demands on memory and CPU power, as it does not contain many of the unnecessary functions found in other languages.
WAP technology
The Wireless Applications Protocol (WAP) arises from the need for industry leaders to create an open standard that allows advanced mobile applications to be offered. WAP takes into account the limiting factor of the mobile network, the need to compress the data, the waiting time, the limited bandwidth and the limitations in the terminals. This development, which benefits and improves the use of wireless connections, has motivated the health sector to develop new services that guarantee better care and patient care. What these telemedicine projects seek is greater collaboration with primary care, especially in areas where accessibility is more limited or in rural areas. What’s more,
WAP definition
WAP is a unified solution for existing and future value-added services. The protocol includes specifications for the OSI session and transport tower layers, as well as security functionalities. WAP also defines an application environment. It is scalable, thus allowing applications to have the screen capabilities and network resources according to their needs and in a large number of types of terminals. The services may be applicable to single-line displays or much more complex terminals. Like any standard, the advantages are multiple when developing applications, manufacturing terminals or structuring the network.
It was in 1994 when Alai Rossmann, a 44-year-old mathematician former Apple employee, founded Libris (later renamed Unwired Planet and, prior to its successful IPO, changed its name to Phone.com again), that he had a vision that Many called it bold and others impossible: Bringing the Internet to cell phones.
For many, the best idea that Román had to advance his vision came after secret meetings at Ericsson headquarters in Sweden and AT&Theadquarters in Seattle: converting the technology with which he had created the first microbrowser and the software that was necessary to run in the networks of the cell phone operator, in a standard.
Thus was born in 1997 the WAP Forum, an entity founded by Phone.com, Ericsson, Nokia and Motorola, and in which today more than two hundred companies from all over the world participate. The first version of the WAP, was not implemented in any phone but served to realize the need to improve various features. Version 1.1, has already been adopted by 75% of mobile manufacturers in the world, whose new phone models “WAP” begin to break into the market, and recently in June of the 2000 left the new version 1.2.
It can be said that WAP, the Wireless Application Protocol, emerges as the combination of two technologies that have grown and spread widely in recent years: Wireless Communications and the Internet.
Wireless environment of WAP applications
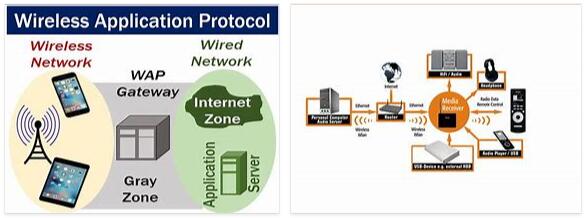
The WAP application wireless environment works as follows. In the first place we have the WAP device, which can be a mobile phone, a PDA or ultimately any device that can act as a WAP browser and therefore has the WAP protocol incorporated.
From this device we can access a specific service or application that is on an Internet server, just by entering its URL. Our WAP device will connect to our telephone operator through one of the different bearers (carriers) available, for example SMS (Short Messages Service), and will send (through the WAP protocol) the information to the WAP Gateway, which will be connected to a SMSC (Short Messages Service Center) and you can receive the request from our device.
Once the request is received, it will translate the request into a conventional HTTP request with the specified URL and send it to the web server. The server will be in charge of returning the object specified by the URL, which can be either a static file, as in the case of a WML program, or a file dynamically generated by means of a CGI. In any case, this server will add an HTTP header to the WIM file or to the CGI result, so that it can be sent correctly over the Internet.
Once the WAP Gateway picks up the file, it verifies the header, encodes the WML and sends a response to the request from the mobile device containing the encoded WML. When the device receives the information, it executes the program.
Most of the WAP Gateways allow access to conventional HTTP information by translating the Web page from HTML to WML, thus allowing access to all the information on the network, although logically with the disadvantage of a small screen such as the case of a mobile phone.
Therefore, the WAP architecture involves three main systems (mobile WAP, WAP Gateway and a conventional HTTP server) and two different means of communication: the wireless network and the Internet.
WAP operation
- The user requests the WAP page they want to view.
- The mobile’s micro browser sends the request with the address (URL) of the requested page and the information about the subscriber to the WAP Gateway (software capable of connecting to the mobile telephone network and the Internet).
- The Gateway examines the request and sends it to the server where the requested information is located.
- The server adds the relevant http or HTTPS information and sends the information back to the Gateway.
- At the Gateway, the server’s response is examined, the WML code is validated for errors, and the response is generated and sent to the mobile.
The micro navigator examines the information received and if the code is correct it displays it on the screen
WAP Technology Protocols
- WAP Protocol Stack
The WAP architecture provides a “scalable and extensible environment for developing applications for mobile devices.” To do this, it defines a layered structure, in which each layer is accessible by the upper layer as well as by other services and applications through a set of well-defined and specified interfaces.
- Wireless Application Environment (WAE)
General purpose Wireless Application Environment based on a combination of WWW and mobile technologies, its objective is to provide an interoperable environment to build applications that work on different platforms. This layer contains the micro-browser and is where the WML and WMLScript languages are specified, as well as the WTA and WTAI functionalities for telephone services.
- Wireless Session Protocol (WSP)
It provides the application layer with two interfaces consisting of session services (Session Layer), one connection-oriented that operates over WTP and the other non-connection-oriented that operates over WDP. It currently provides HTTP / 1.1 functionality optimized for wireless environments.
- Wireless Transaction Protocol (WTP)
(Transaction Layer) It runs on a data gram service and forms a thin layer oriented to transaction, it operates efficiently on secure and non-secure networks.
- Wireless Transport Layer Security (WTLS)
The Wireless Transport Security Layer (WTLS) is a protocol based on the TSL standard which is based on the SSL3.0 specification published by Netscape, and used in the Web environment for the proportion of security in the realization of data transfers. WTLS has been specially designed for the WAP transport protocols and optimized for use in narrow band communication channels.
WTLS offers the following security features
Data integrity: ensures that the data sent between a terminal and a server cannot be modified by third parties.
Privacy: Ensures that the transmitted data cannot be recovered by third parties that may intercept the data flow.
Authentication: WTLS has facilities to establish the authenticity of the terminal and the server.
Protection Service – Service Repudiation: WTLS has facilities to detect and reject data that is forwarded or not verified satisfactorily. WTLS can also be used for secure communications between terminals. Applications can enable or disable WTLS depending on the security requirements and characteristics of the transport network.
- Wireless Datagram Protocol (WDP)
The transport layer in WAP, referred to as WDP, operates on data transport services supported by various types of networks. WDP offers a consistent service to the upper layers communicating them transparently independent of the carrier layer, allowing applications to be independent of the wireless network.
- Service Carriers (Bearers)
WAP is designed to operate over a variety of different bearer services, including SMS, Circuit switched Data (CSD), and packet data among others. The carriers offer different levels of quality of service regarding throughput, error rate and delays, WAP is designed to compensate or tolerate variations in the level of service.
Other services and applications
WAP enables other applications and services to use the WAP stack through well-defined interfaces, this allows using WAP for applications that are not specified by WAP.
The current state of the world of wireless communications has improved or eliminated many of the limitations that these services presented, one of those cases is the development of the Wireless Applications Protocol (WAP), which defines an application environment that allows telephones to mobile phones, Palmtops (handheld computers), laptops, and any other, access networks with a global understanding.
From the point of view of health, the monitoring of vital signs through telemedicine represents a great advance in hospital services, since they are carried out in a transparent way for the patient, where the instruments installed at home measure different electrophysiological parameters and the They are sent to the hospital, where they are controlled by the doctor without the patient having to intervene, avoiding discomfort and at the same time that the patient, wherever he is, feels that he can always count on a professional who can help him.
On the other hand, what is intended is to exploit existing technological resources, such as the mobile phone, which is an instrument that more and more people use and that has resources that allow continuous control and communication between the patient and their doctor., which will be strengthened with the approach of mobile telephony and the Internet.